A consolidated view of your environment, built from the tools you already use. Plug & play data aggregator free trial
Test — see — decide.
14 days to see what your IT really hides.
Plug in your sources and see the value right away — the named list of machines without EDR, of admins without MFA, of critical servers without backup. No salesperson to listen to. No meeting to schedule.*
*No data on hand, or want to look before plugging in? A ready-to-use set of sample data is available in the test environment.
- Your data, or sample data
- Secure test environment
- One-click deletion
If you don’t see the value
in 14 days,
we don’t deserve your attention.
But if you test —
you’ll know.
— THE OVERVIEW TEAM
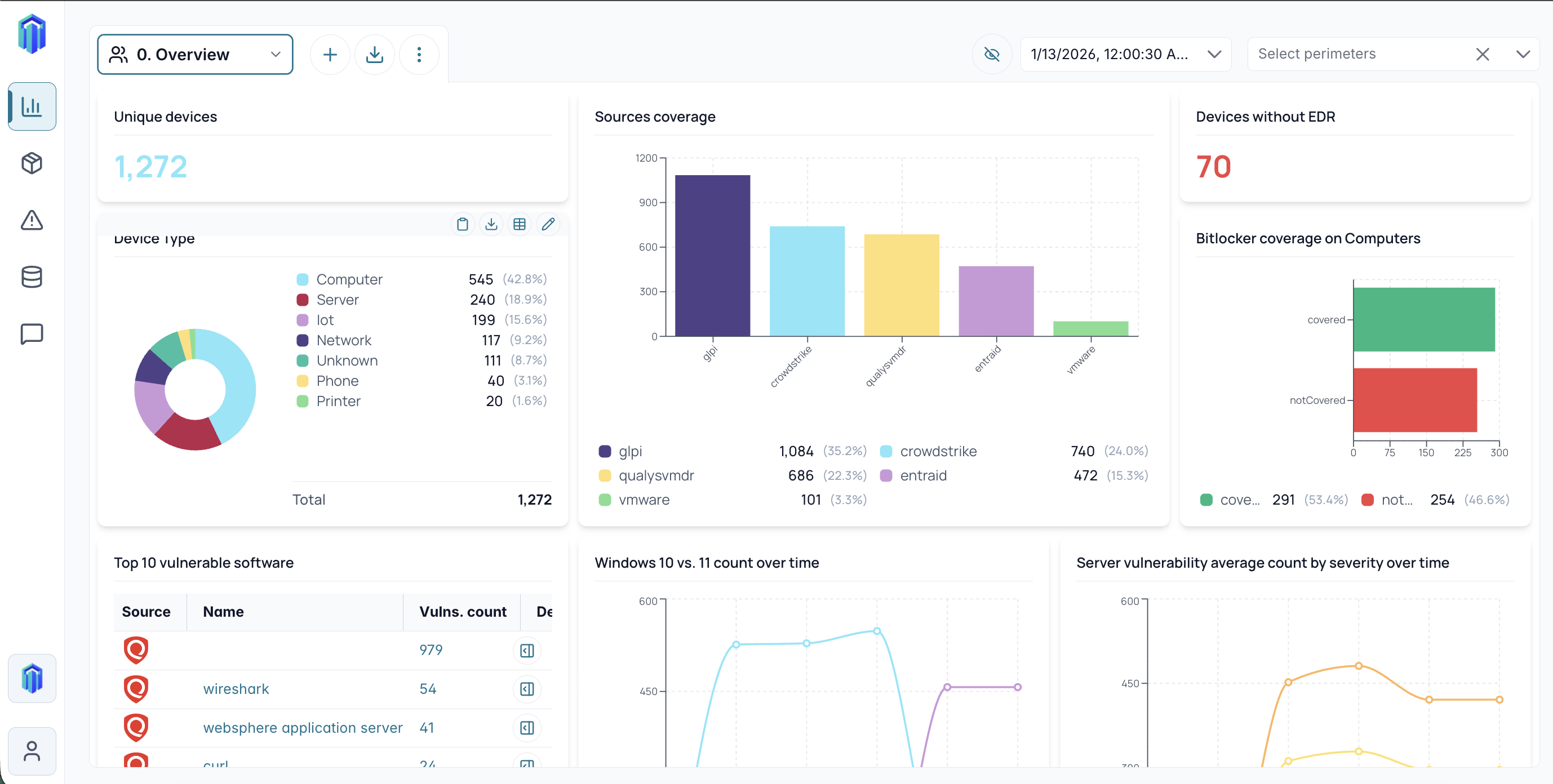
Five dashboards, 24 indicators, your named lists.
No more generic dashboard to explore without knowing where to start. You tick what concerns you at signup, and the matching pre-configured KPIs load on their own — with your data, or with a realistic set of sample data to look before plugging in.
Do my security tools cover the entire estate?
Cross-referencing your inventories with your agents reveals the blind spots — missing EDR, failing backups, unencrypted workstations, Intune compliance.
- Machines without EDR~55 · 8%
- Servers with no backup at all~80 · 39%
- Failed or warning backups9 + 32
- Unencrypted Windows workstations~27 stations
- Intune non-compliant assets37 + 33
Who can connect to my systems, and with what privileges?
Privileged accounts without MFA, departed contractors still active, cross-tenant admins (AD × Azure AD) — OverView cleans up what your directories don’t reveal separately.
- Azure AD admins without MFA~19 / 109
- AD Domain Admins without Azure MFA~4 accounts
- AD PasswordNotRequired accounts~3 accounts
- Expired contractors still Enabled~5 accounts
- Ghost AD accounts~5-10
What do I need to migrate, and when?
Not a percentage, a dated list — workstation by workstation, server by server. How long the OS has been out of support, what runs on it, and who uses it. The kind of info your insurer will ask for.
- Active Windows 7 workstations~36 stations
- Windows 2008 R2 / 2012 R2 servers~26 srv.
- Windows 2016 servers~16 srv.
- Windows 10 stations (Win11 migration)~105 stations
- VMware VMs on obsolete hardware~10 VMs
Which flaws to tackle first, today?
Not the 57,000 CVEs from your scanner. The handful in CISA’s KEV catalog (actively exploited), present on your critical assets, with a public exploit available. Prioritization that holds up in a board meeting.
- Active KEV CVEs on critical assets~10-15
- Public-IP VMs + KEV CVE~3-5 VMs
- Top CVEs by impacted asset countauto
- Critical CVEs with available fixauto
Can I trust my inventories before acting?
The foundation of everything else. GLPI says 1083, your EDR says 715, your EntraID says 472 — each source sees a different subset of the estate. OverView shows where the gaps are, and who owns what.
- Uniqueness gaps across sources1083 / 715 / 472
- Assets seen by a single source~25-30
- Assets missing from CMDB~25-30
- Inactive legacy assets > 6 months~15-20
- Assets with no identified user~5-8
Reconcile. Act. Report.
OverView doesn’t rest on a single promise. Three value steps you go through in order — from consolidation to action, then to governance. Each step unlocks the next.
Reconcile your inventories.
Before any anomaly detection, OverView ends the debates over numbers. IT, security, support and infra teams finally share a single source of truth, consolidated from the tools you already use.
"No more cross-checked spreadsheets. No more ping-pong between five consoles."
Act with operational dashboards.
Building on the consolidated inventory, each team builds its own dashboards to manage its scope and prioritize actions. Action-oriented, not contemplation. Aligned with your security policy. Per team, per use case.
"I know where to start — and I show it to my team."
Report to your leadership.
OverView consolidates key indicators in a synthetic view designed to climb the decision chain: CIO, board, cyber insurer, due diligence, audits. Key figures, PDF exports, target widgets.
"I finally have a dashboard I can present."
Get my test environment.
90 seconds to pre-register. Your access will be sent by email on June 1st, when OverWeek opens. 14 days of full access starting from receipt.
Security, GDPR, hosting, data purge, pricing — all the answers are presented to you when creating the environment, exactly when you need them.
We’re not asking you to take our word for it. We’re asking you to come see.
Oh that’s great! We see all the work we have to do, and we can track progress.
OverWeek beta tester
57,000 vulnerabilities. 10 minutes to know which ones to fix first.
OverWeek beta tester
I was already able to fix things, so it’s interesting. It’s already paying off.
OverWeek beta tester